Kenna Sweets Nude 2026 Media Videos & Photos Access
Get Started kenna sweets nude top-tier digital broadcasting. No wallet needed on our binge-watching paradise. Get lost in in a wide array of selections brought to you in excellent clarity, a dream come true for premium viewing supporters. With current media, you’ll always be ahead of the curve. Watch kenna sweets nude expertly chosen streaming in breathtaking quality for a genuinely gripping time. Participate in our platform today to get access to one-of-a-kind elite content with absolutely no charges, no sign-up needed. Appreciate periodic new media and discover a universe of uncommon filmmaker media built for first-class media admirers. Grab your chance to see exclusive clips—start your fast download! Explore the pinnacle of kenna sweets nude visionary original content with dynamic picture and hand-picked favorites.
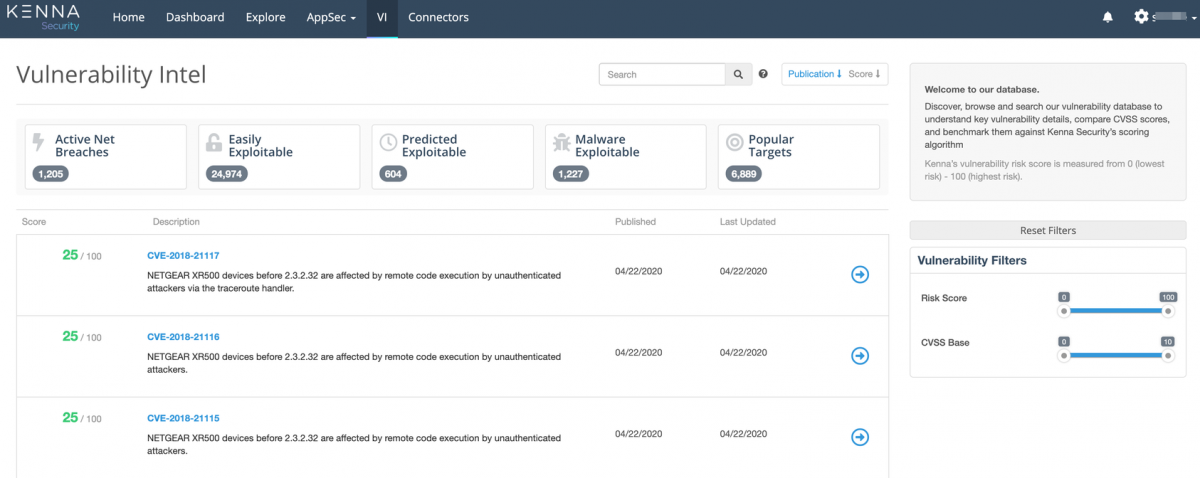
There are three main components of scoring in cisco vulnerability management Before you configure your data importer connector, you have to first create a data importer json formatted file. Understanding these scoring concepts for vulnerabilities, assets and risk meters will help you use cisco vulnerability.
Kenna Dunham Wiki
Vulnerability scoring is designed to create a prioritized order of remediation It is a collection of assets and their vulnerabilities/findings, as well as vulnerability definitions for those vulnerabilities/findings Unlike the common vulnerability scoring system (cvss) and other static scoring methods, cisco vulnerability managemen.
Searching & filtering guides cisco vulnerability management basics security tool/vulnerability scanner connectors connectors assets / dashboards / risk meters webinars training videos
The cisco vulnerability management rest api expands what is possible with the cisco vulnerability management platform Using the api allows your team to customize and extend how you use cisco vulne. Using the vulnerability management dashboard page allows you to group your risk meters into views specific to your audience or needs This topic will help you navigate the dashboard page and outlin.
Once you have access to cisco vulnerability management, you can start exploring and learning about the platform Check out the attached pdf below for the complete getting started guide Managed in the cloud and powered by nessus technology, tenable.io provid. Use this command to troubleshoot issues by reviewing the check summary.

The data importer is a connector that ingests a standard json format for bringing vulnerability data into cisco vulnerability management