Sha'carri Nude 2026 Folder Video/Photo Access
Open Now sha'carri nude elite online playback. Freely available on our video archive. Surrender to the experience in a large database of hand-picked clips unveiled in HD quality, essential for high-quality streaming admirers. With content updated daily, you’ll always know what's new. Encounter sha'carri nude tailored streaming in impressive definition for a deeply engaging spectacle. Register for our creator circle today to stream solely available premium media with no charges involved, no sign-up needed. Appreciate periodic new media and discover a universe of uncommon filmmaker media optimized for first-class media addicts. Make sure you see distinctive content—get it fast! Discover the top selections of sha'carri nude specialized creator content with rich colors and unique suggestions.
Web self registration ussd self registration assisted enrolmentfrequently asked questions It takes an input message, such as a text, file, password, or any data input, and runs it through a mathematical process to generate a unique hash value known as a message digest or hash digest. They differ in the word size
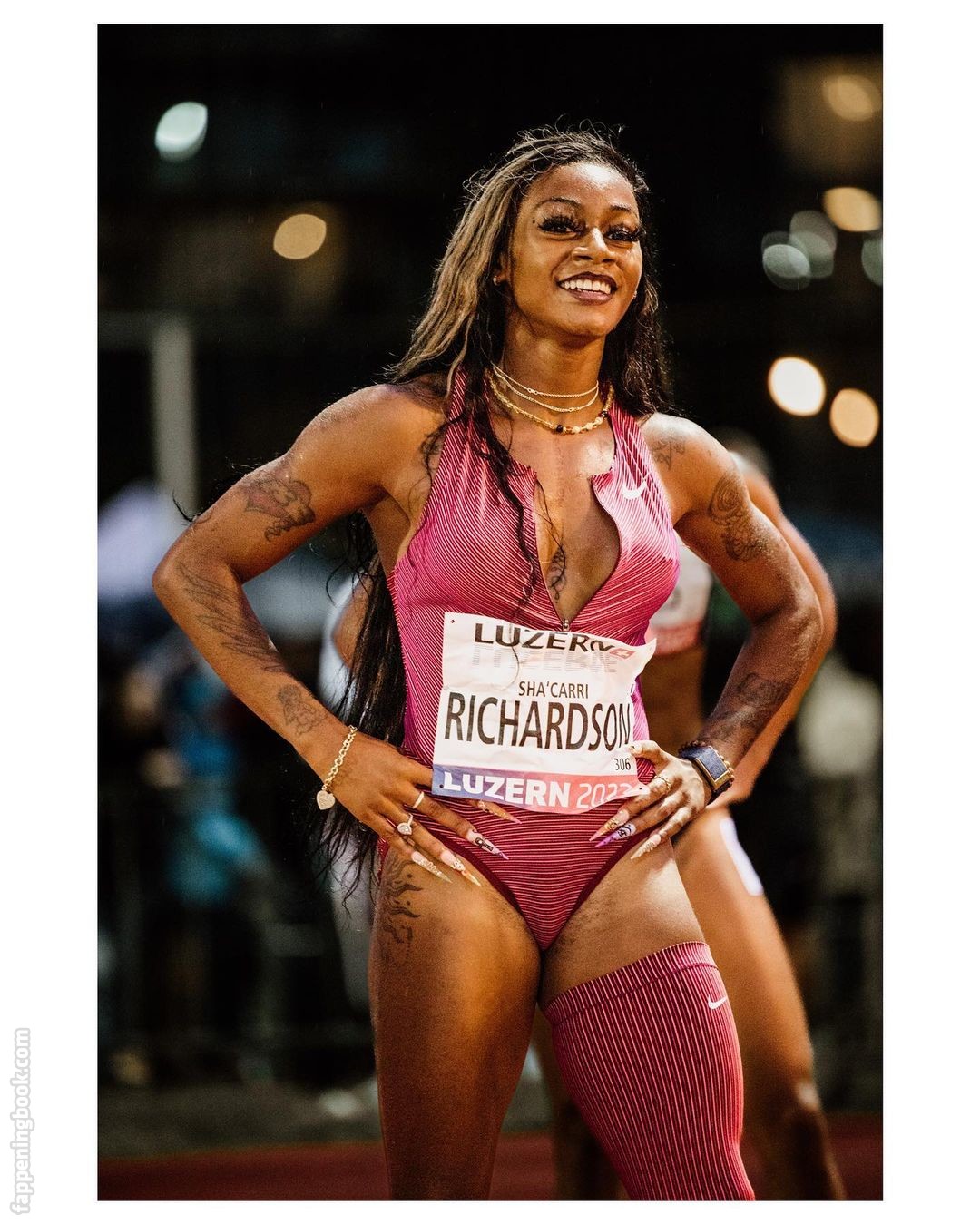
Sha'Carri Richardson / carririchardson_ Nude, OnlyFans Leaks, Fappening
A secure hashing algorithm, or sha, changes data by creating a hash digest unique to each plaintext message Sha stands for secure hash algorithm, a cryptographic function developed to protect sensitive data Sha is an acronym for secure hash algorithm, a family of cryptographic hash functions designed by the national security agency (nsa)
This cryptographic hash function plays a critical role in ensuring the integrity and security of digital data.
Hashing is used for data integrity verification and to detect any unauthorized modification or tampering and can ensure the digital document's authenticity Secure hash algorithms (sha) is one of the cryptography technology and uses hashing for plaintext to message digest conversion. Secure hash algorithms, also known as sha, are a family of cryptographic functions designed to keep data secured It works by transforming the data using a hash function
An algorithm that consists of bitwise operations, modular additions, and compression functions.